Table of Contents
Basic authentication in the Microsoft 365
For many years, applications have used Basic authentication to connect to servers, services, and API endpoints. Basic authentication simply means the application sends a username and password with every request, and those credentials are also often stored or saved on the device.
Microsoft is removing the ability to use Basic authentication in Exchange Online for:
- Exchange ActiveSync (EAS)
- POP
- IMAP
- Remote PowerShell
- Exchange Web Services (EWS)
- Offline Address Book (OAB)
- Outlook for Windows and Mac.
Microsoft’s also disabling SMTP AUTH in all tenants in which it’s not being used. If you want to check SMTP AUTH in your organization let’s visit this post.
When will this change take place?
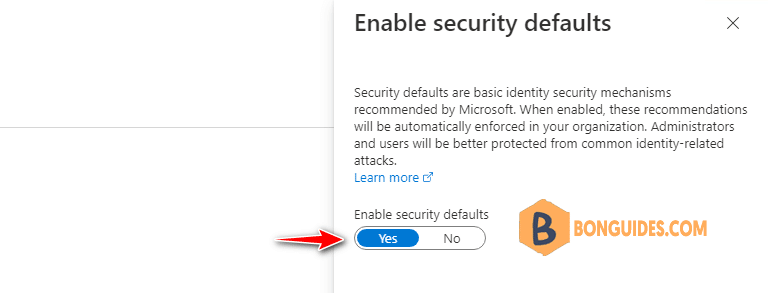
Microsoft’s already started making this change. New Microsoft 365 tenants are created with Basic authentication already turned off as they have Security defaults enabled
In September 2021, Microsoft announced that effective October 1, 2022, they will begin disabling Basic authentication for Outlook, EWS, RPS, POP, IMAP, and EAS protocols in Exchange Online. SMTP Auth will also be disabled if it is not being used.
POP, IMAP, and SMTP AUTH
In 2020, Microsoft released OAuth 2.0 support for POP, IMAP, and SMTP AUTH. You can update your client apps to support these authentication types. Unfortunately, There is no plan for Outlook clients to support OAuth for POP and IMAP.
In some cases, if your organization still required POP/IMAP, you must using a third-party app which supports Modern Authentication to connect to Exchange Online over POP or IMAP protocol.
Check Basic Authentication Enabled or Disabled
Firstly, if Security Defaults are enabled in your tenant, it means all legacy authentication at the tenant level for all protocols with no exception.
Security Defaults are enabled mean the basic authentication is disabled completely in your tenant across all protocol included SMTP Auth.
If you have authentication policies configured in your Office 365 tenant, you can display the current settings and protocols that are allowed to use Basic Authentication. Use the following PowerShell command:
Before you begin, let’s connect to Exchange online PowerShell.
In our case, we have only one policy and BasicAuth is disabled for all apps.
PS C:\WINDOWS\system32> Get-AuthenticationPolicy
AllowBasicAuthActiveSync : False
AllowBasicAuthAutodiscover : False
AllowBasicAuthImap : False
AllowBasicAuthMapi : False
AllowBasicAuthOfflineAddressBook : False
AllowBasicAuthOutlookService : False
AllowBasicAuthPop : False
AllowBasicAuthReportingWebServices : False
AllowBasicAuthRest : False
AllowBasicAuthRpc : False
AllowBasicAuthSmtp : False
AllowBasicAuthWebServices : False
AllowBasicAuthPowershell : FalseFor security purposes, you must create a separate policy with different Basic Auth permissions for specific protocols and assign it to users using the legacy application.
Note: The custom policies allow basic authentication will stop working when Microsoft turns off basic authentication globally on October 1, 2022.
New-AuthenticationPolicy -Name "BasicAuth_Allow_POP"
Set-AuthenticationPolicy -Identity "BasicAuth_Allow_POP" -AllowBasicAuthPop:$true
Set-User -Identity [email protected] -AuthenticationPolicy "BasicAuth_Allow_POP"
PS C:\WINDOWS\system32> Get-AuthenticationPolicy -Identity BasicAuth_Allow_POP
AllowBasicAuthActiveSync : False
AllowBasicAuthAutodiscover : False
AllowBasicAuthImap : False
AllowBasicAuthMapi : False
AllowBasicAuthOfflineAddressBook : False
AllowBasicAuthOutlookService : False
AllowBasicAuthPop : True
AllowBasicAuthReportingWebServices : False
AllowBasicAuthRest : False
AllowBasicAuthRpc : False
AllowBasicAuthSmtp : False
AllowBasicAuthWebServices : FalseAlso, note that there is another OAuth2ClientProfileEnabled option in the organization settings, which determines whether Modern Auth is enabled for the tenant:
If OAuth2ClientProfileEnabled = False, it means that modern authentication is disabled.
PS C:\WINDOWS\system32> Get-OrganizationConfig | ft OAuth*
OAuth2ClientProfileEnabled
--------------------------
TrueEnable basic authentication for SMTP
Some organizations still need SMTP basic authentication to sending emails through printers or scanners. So, they need SMTP AUTH using legacy protocol.
Microsoft doesn’t has a plan to disable basic authentication on SMTP. But SMTP Auth will also be disabled if it is not being used in your organization.
To check basic authentication for SMTP is enabled or disabled, let’s run the following command:
PS C:\> Get-TransportConfig | Format-List SmtpClientAuthenticationDisabled
SmtpClientAuthenticationDisabled : TrueSmtpClientAuthenticationDisabled property is True means the basic authentication for SMTP is already disabled. To enable it, let’s run the following command.
Set-TransportConfig -SmtpClientAuthenticationDisabled $falseMicrosoft highly recommend that you disable SMTP AUTH in your Exchange Online organization, and enable it only for the accounts (that is mailboxes) that still require it. Enable SMTP AUTH for specific mailboxes