Table of Contents
PowerShell Remote Connection with SSH
The built-in SSH client appeared in Windows 10 and Windows Server 2019. It can be used to securely connect to Linux/UNIX servers, VMWare ESXi hosts and other devices instead of Putty. The native Windows SSH client is based on the OpenSSH port and is preinstalled in Windows starting from Windows 10 build 1809.
We can use SSH in PowerShell to establish a remote connection to another computer or server. This can be between Windows computers or Windows-Linux and vice versa.
The most common way to use SSH in PowerShell is as an SSH Client. Assuming that you keep your Windows up-to-date you should have SSH enabled by default. You can simply check it by opening PowerShell and type the following command:
# type ssh and press enter
ssh
# Result:
usage: ssh [-46AaCfGgKkMNnqsTtVvXxYy] [-B bind_interface]
[-b bind_address] [-c cipher_spec] [-D [bind_address:]port]
[-E log_file] [-e escape_char] [-F configfile] [-I pkcs11]
[-i identity_file] [-J [user@]host[:port]] [-L address]
[-l login_name] [-m mac_spec] [-O ctl_cmd] [-o option] [-p port]
[-Q query_option] [-R address] [-S ctl_path] [-W host:port]
[-w local_tun[:remote_tun]] destination [command]You can check the OpenSSH client is installed or not:
Get-WindowsCapability -Online | ? Name -like 'OpenSSH.Client*'# Output
Name : OpenSSH.Client~~~~0.0.1.0
State : InstalledIf not (State: Not Present), you can install it using the following PowerShell command:
Add-WindowsCapability -Online -Name OpenSSH.Client*Password-based authentication
With PowerShell open you can connect to a remote server or network device with a single command:
ssh <username>@<host_ip_address># For example:
ssh [email protected]When you connect to a machine using SSH. For the first time you will need to accept the host’s key. Just type yes then hit Enter.
PS C:\> ssh [email protected]
The authenticity of host '10.10.6.22 (10.10.6.22)' can't be established.
ED25519 key fingerprint is SHA256:DFhYvYIS0O+SNI53un5Cbn4WB3YbxP6USGKbSp/XPEA.
This key is not known by any other names
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '10.10.6.22' (ED25519) to the list of known hosts.
[email protected]'s password:
Welcome to Ubuntu 22.04.1 LTS (GNU/Linux 6.2.0-33-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
206 updates can be applied immediately.
1 of these updates is a standard security update.
To see these additional updates run: apt list --upgradable
Last login: Sun Oct 1 04:19:29 2023 from 10.10.5.52
leo@ub22:~$If you have SSH running on a different port than the default port 22, then you can change the port number with the -p flag:
ssh <username>@<host_ip_address> -P <port_number>
#For example
ssh [email protected] -p 2222
Key-based authentication
Alternatively, we can authenticate using public-private keys. The advantage of this method :
- More secure because using keys instead of clear text password.
- Supports multiple encryption protocols.
- Secure private keys using passphrase.
- Automation authentication flow with ssh agent to manage all private keys.
Create a SSH Key Pair for SSH Authentication
1. First, launch a PowerShell window.
2. Inside PowerShell, run the ssh-keygen command. The -t parameter tells OpenSSH what type of SSH key should be created. Here we go with the rsa type.
ssh-keygen -t rsaGenerating public/private rsa key pair.
Enter file in which to save the key (C:\Users\admin/.ssh/id_rsa):
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in C:\Users\admin/.ssh/id_rsa
Your public key has been saved in C:\Users\admin/.ssh/id_rsa.pub
The key fingerprint is:
SHA256:VW5ljf///nCFNw6ts450VISE/F+hx9dlgvtY9xZW1E0 admin@win11
The key's randomart image is:
+---[RSA 3072]----+
| . +o+*E|
| =.++.B|
| . +.o==|
| . ..o+**|
| S *=+O|
| o =o*|
| . +.oo|
| . o oo.|
| ..o .*|
+----[SHA256]-----+3. A new folder named .ssh will be created within your user’s home folder (C:\Users<username>\.ssh). Two files have been created inside that folder.
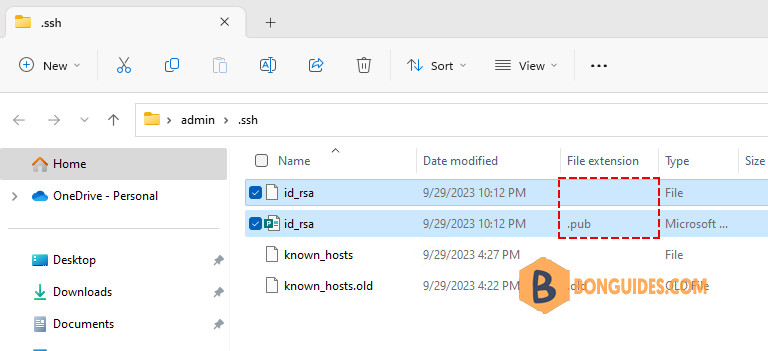
The difference between the two is the file extension (which is not shown by default in Windows Explorer).
- The id_rsa file without extension is the private key – which you should guard like your own wallet. It can also be password-protected (as prompted in the ssh-keygen command above).
- The id_rsa.pub file is the public counterpart of your private key. It needs to be installed on the target server(s) where you want to login using SSH.
Launch SSH agent (optional)
A SSH agent is a small program which runs in the background and loads your private key with the password into memory. This allows to use the ssh command without always having to enter the passphrase again.
You can check whether the service is already running or not:
PS C:\> Get-Service ssh-agent
Status Name DisplayName
------ ---- -----------
Stopped ssh-agent OpenSSH Authentication AgentThen enter the following commands in the administrator PowerShell window:
Get-Service ssh-agent | Set-Service -StartupType Manual
Start-Service ssh-agent
Get-Service ssh-agentStatus Name DisplayName
------ ---- -----------
Running ssh-agent OpenSSH Authentication AgentThe ssh-agent is now running. use ssh-add to load your own private key into the SSH agent:
ssh-add $env:USERPROFILE\.ssh\id_rsa#Output
Identity added: C:\Users\admin\.ssh\id_rsa (admin@win11)Install the public key on the remote server
1. Remember the mentioned public key? Now it is time to look at the contents. Using the Windows Explorer, navigate to your .ssh folder. Or you can use Get-Content cmdlet to get its content.
Get-Content $env:USERPROFILE\.ssh\id_rsa.pub2. Open the id_rsa.pub file with a text editor. Notepad will do. This shows the content of the public key, which is a long line of a text:
ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABgQC5786CyQZizFqWs/YLCOFcougR1wZBG2yHFjswSACeJMO8DV3lGPjmOXMLf5z2QQy1mZHUW7t9J7EWzDj54lr7VNd+CwW2Jo0inRAP3+IzxcELwYBwJmfSj+KbWMsJF7Q8zden4t8G1jlFXE1Md8O3JUH4MyM4W7Ze9QmOy1fp8OftCyx4LPTWgbC1eqtwmck5AZgrfa8039E61LH+dKapcvgj5DgAE8Kco8zg/2RZBGrRWfa8FANr3fcfdaFN0mH3xQpcgO8/EfJhzTDmBVlFa2I5pkAFHHMvjcSWzK9fUzTIaPYWm+nNTQl/KSuW1kZi3sVfzcfCXEkUrCKAqc1OOQK8nvCm4578yCpb0gS6ge/VLGp5ZpUeOsvtN0JckGT6MBSr7VfheVABueflCm/hj9Nmouvf/oQfdjs4g+too99+ZJpIv6IWJHY4Kd2HettwnvwCam97KaEKEvIpyTQTjMhnQXPCKsPAk2sqH1VM9CwfyPfDoHZv4XqBLK3j+QM= admin@win113. SSH to the remote server. This time, you still need to use password authentication.
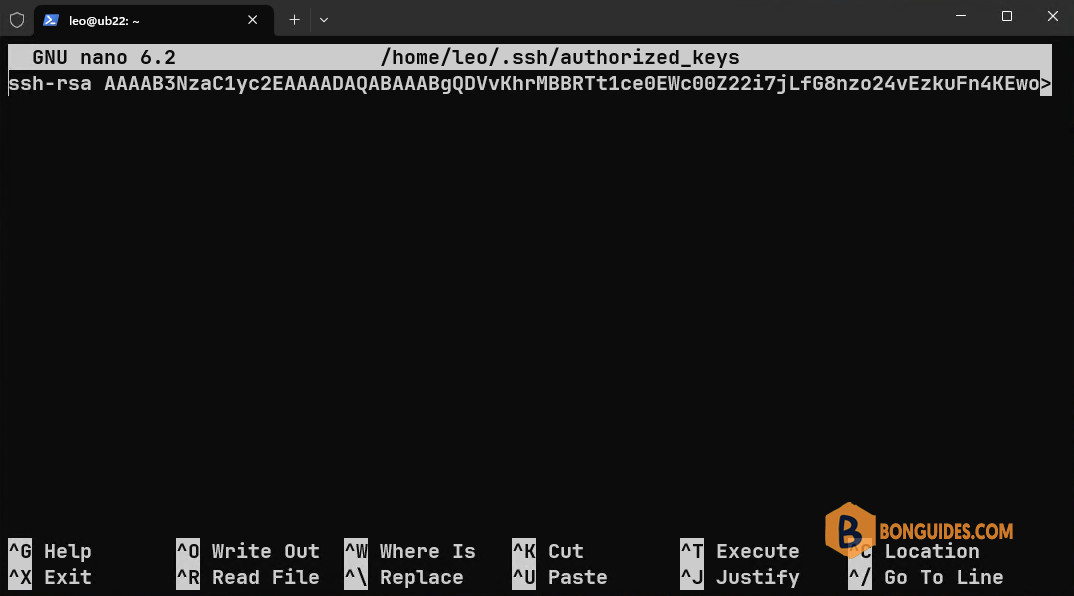
4. Create a new file named ~/.ssh/authorized_keys on the remote server using your favorite text editor.
mkdir ~/.ssh
nano ~/.ssh/authorized_keys5. Copy content of the public key from notepad to the newly created file.
6. Check then enable public key Authentication if it not enabled yet. The settings for OpenSSH server is located in /etc/ssh/sshd_config.
sudo nano /etc/ssh/sshd_config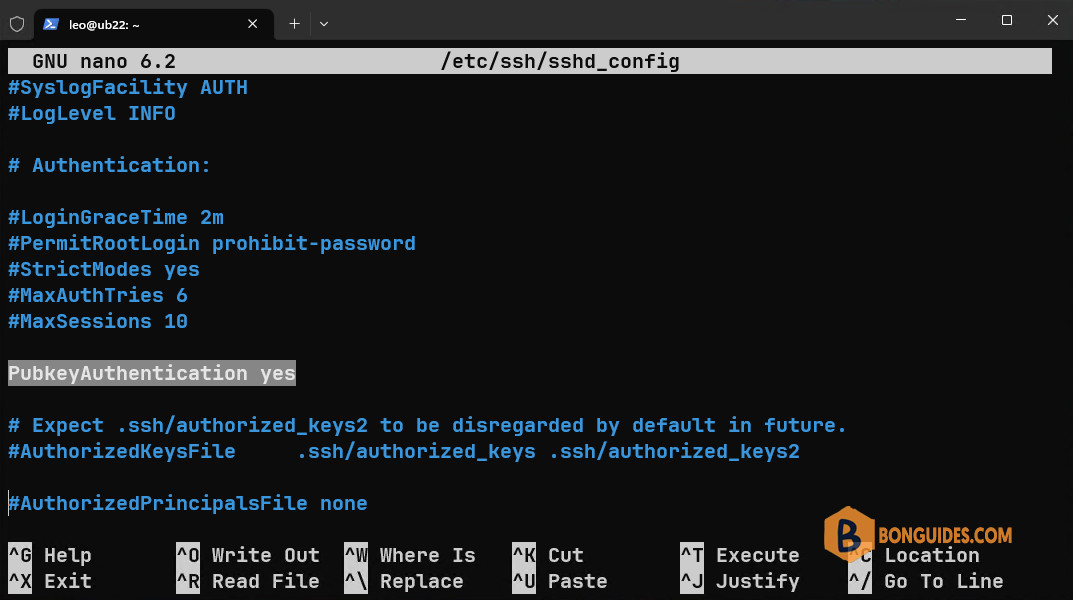
7. Finally, restart the SSH service.
sudo systemctl resrart sshConnect to a remote SSH server
Now that we have created a key, enabled ssh agent and placed the public key on the target server, we can initiate a ssh connection.
#Connect without ssh-agent
ssh [email protected] -i C:\Users\admin\.ssh\id_rsa#Connect with a private key id loaded using ssh-agent
ssh [email protected]Not a reader? Watch this related video tutorial:
Related Titles:
- How to Use PowerShell to SSH into a Linux Machine
- Connecting to Linux from Windows Using PowerShell and SSH
- PowerShell SSH Guide: Connect to Linux in Minutes
- SSH into Linux with PowerShell: A Complete Tutorial
- Step-by-Step: Using PowerShell to Access Linux Servers
- How to Setup SSH on PowerShell for Linux Connections
- Mastering SSH in PowerShell for Linux Admins
- Easy Guide: Connect to Linux Using PowerShell and SSH
- How to Securely Connect to a Linux Server with PowerShell
- Windows to Linux: SSH Connections with PowerShell Explained
- Using OpenSSH in PowerShell to Manage Linux Servers
- The Ultimate PowerShell SSH Guide for Linux Access
- Beginner’s Guide: SSH into Linux from Windows PowerShell
- Remote Linux Management with PowerShell SSH
- How to Connect to Linux Remotely Using PowerShell and SSH
Keywords:
PowerShell SSH, connect to Linux with PowerShell, SSH from Windows to Linux, PowerShell SSH tutorial, how to SSH with PowerShell, connect to Linux server, OpenSSH PowerShell, SSH in PowerShell, Linux remote access, Windows SSH client, SSH setup PowerShell, PowerShell Linux connection, remote Linux management, SSH Windows tutorial, secure shell PowerShell
Hashtags:
#bonguides, #PowerShell, #SSH, #Linux, #TechTutorial, #WindowsToLinux, #RemoteAccess, #LinuxServer, #OpenSSH, #CommandLine, #TechGuides, #SecureShell, #ITSupport, #TechTips, #LearnTech





You have:
If you have SSH running on a different port than the default port 22, then you can change the port number with the -p flag:
ssh @ -P
#For example
ssh [email protected] -p 2222
You have uppercase for -P flag.
Seems that it should be lowercase -p.
Thank you for your comment, in Windows, it is not-case sensitive.
Thanks for the guide!